The standard describes the requirements for the implementation, realisation, maintenance, documentation and continuous improvement of an information security management system (ISMS). The confidentiality, integrity and availability of information form the core of this. This ensures that your data is used optimally and kept safe. The standard also ensures the availability of all systems that are relevant to the company's processes. The selection of appropriate security mechanisms ensures protection of all assets and value chains.
Advantages of certification according to DIN ISO / IEC 27001
- Identify risks at an early stage and remedy them with appropriate measures.
- Systematically uncover weak points.
- Ensure reliable protection of confidential data and information.
- Reduce costs (process/financing/IT costs).
- Promote the development of a safety culture in your organisation.
- Increase the competitiveness of your company.
- Create or increase the trust of your prospects, customers and business partners.
ISO 27001 certification
By certifying the existing information security management system, your company demonstrates that information security requirements and data protection measures have been met and implemented.
Basically, there are two types of certification - directly according to ISO 27001 and on the basis of IT baseline. The prerequisite for both is the existence of an information security management system (ISMS). In addition to the documentation of your company's values and their documentation, possible security risks must be identified, assessed and monitored. If the standard has been implemented, a certification audit must be carried out by a certification body.
Certification according to ISO 27001 can be done for the entire company or only for a specific scope. Further information on certification and recognition of the standard can be found on the website of the German Federal Office for Information Security (German: BSI).

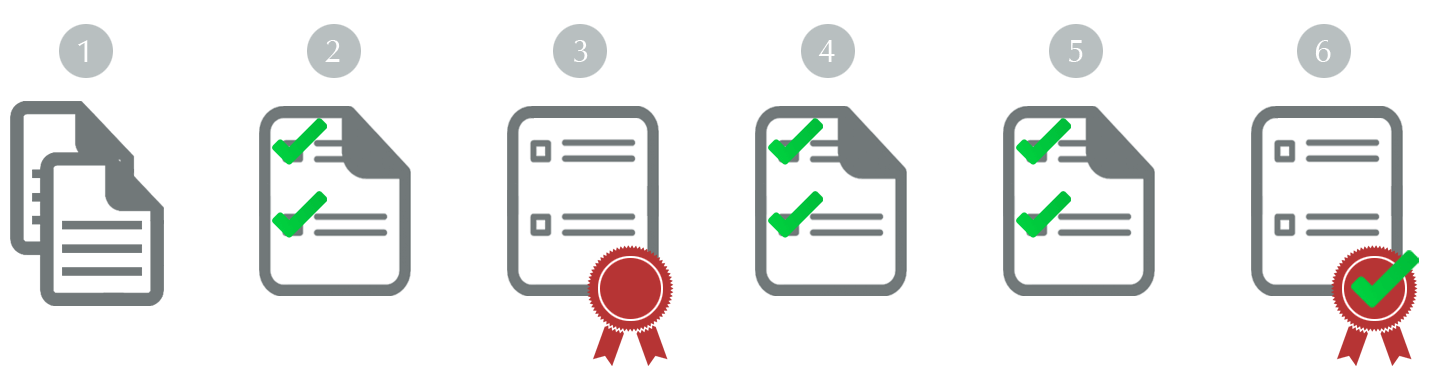
Process of certification according to ISO 27001
To have its information security management system certified according to ISO 27001, your company must go through a multi-stage audit process. This is carried out by one or more independent certified auditors.
- Pre-audit: Examination of all documents for completeness and conformity to standards by the auditor.
- Certification audit: Review of the documentation and the effectiveness of the ISMS in the company, correction of deviations if necessary. Preparation of the audit report incl. evaluation of the management system.
- Issue of the certificate: After a successful audit, the certificate and test seal are issued for a maximum of 3 years.
- Surveillance audits: In the second and third year (1x per year) after certification, the information security management system is checked to ensure that it continues to meet the requirements of the standard.
- Re-certification: After expiry of the 3-year validity of the certificate.
How do you integrate an efficient ISMS?
It is important to understand that information security is not a one-off project, but a continuous process to constantly monitor the level of security in the company and the operational processes. An ISMS supports the company management in implementing appropriate measures to improve information security and thus achieve the security goals. ISO 27001 is one of the standards that provide a reference framework to support the implementation of an ISMS.
Information security should be directly integrated into business processes in order to observe there what information flows and needs to be protected.
Download
Establish procedures and rules according to ISO 27001 in your company to permanently improve information security. The most important functions of the ISMS module can be found in our product flyer.
